Secure data erasure
by Felix Kinaro About 2 min reading time
Secure data erasure aims at removing traces of any data that my have been stored on a drive while leaving the drive usable. Sectors or cells are overwritten with 1's and 0's in order to render the data unrecoverable.
This can be triggered by a wide variety of factors. For instance you want to sell your laptop but you can't risk someone else coming across your photos or documents. Deletion using the Delete option in the right-click context menu does not actually remove the data from the drive. The OS marks the sectors as empty for them to be overwritten the next time something is to be saved to disk.
Data that has been deleted can still be recovered using tools such as Recuva, or TestDisk among many other free and commercial tools. This poses a risk to privacy as anyone with physical access can attempt to snoop by recovering deleted files.
Erasing a hard drive before selling
Most computers have a feature in the Bios to erase a hard drive. This requires interrupting the boot process by pressing Esc, F2 or F10. Consult your device manual on how to access the feature.
Erasing data securely on a Windows system
The easiest option is to use CCleaner and select the wipe free space option n the Tools subsection. .
.
However, Windows has a built-in tool called Cipher which can also be used to securely erase data. The tools also encrypts data, so extra caution would be beneficial in order to avoid unintended actions.
To remove data:
- Open the Command Prompt or PowerShell.
- Type cipher /w:C. The /w parameter tells cipher to overwrite the deallocated data. 'C' represents the drive or partition you want erased. You can also point to a specific folder, such as cipher /w:C:\folder1. How long the process takes depends on the size of the drive you are overwriting. Another benefit is that Cipher may free up additional space.
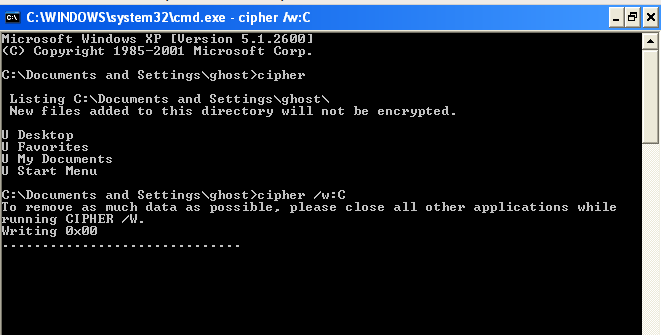
This is best done while you are not actively using your computer, or overnight with no other applications running.
You can refer to the Microsoft docs on cipher here and here too.
Erasing data securely on a Linux system
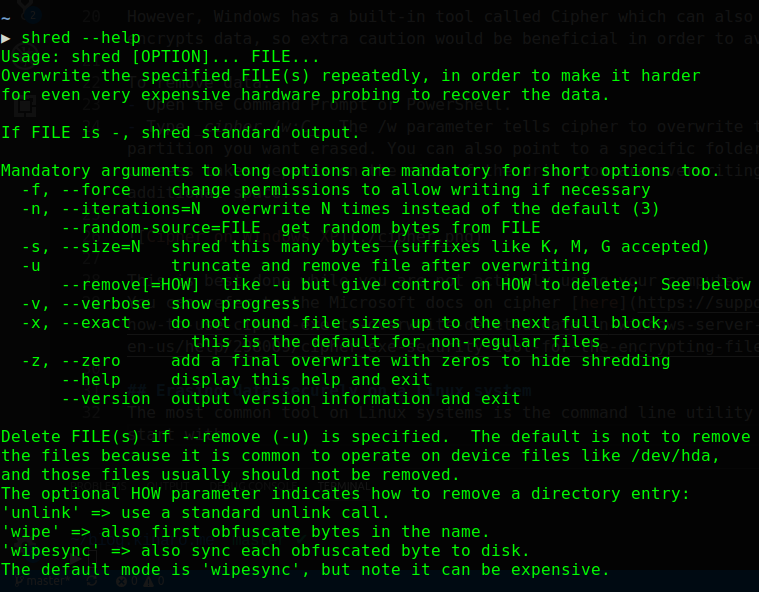
The most common tool on Linux systems is the command line utility shred. The man pages are an excellent point to start with. Type man shred or shred --help in Terminal to access help text.
Shred allows you to choose a source of random data. /dev/urandom is the best source of randomness as it is non-blocking and does not deplete the entropy pool. To overwrite a file and then delete it:
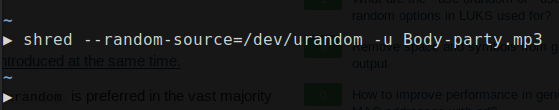
The -u switch tells shred to remove the file after overwriting. You should be careful to avoid removing important files such as disk drives.
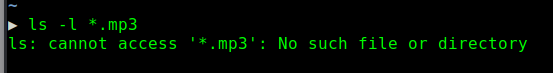
The file has successfully been overwitten and deleted.